The last thing you want to happen with your files is to be held for ransom before you can access them. Unfortunately, many businesses still fall victim of the number one threat in cybersecurity – Ransomware. To protect yourself from these dangerous attacks, it’s critical to know how they work, and what steps you can take to thwart them.
What is a Ransomware
Ransomware is a type of malicious software that infects your computer – it locks and encrypts your files then demands a specific amount of money as ransom to restore access. The ransom is usually paid in bitcoins; once paid, you will receive a decryption key to recover your files.
Ransomware is different from a virus. Viruses infect your files or software and have the ability to affect your device’s performance, delete files, send spam, and even corrupt your hard drive. Ransomware, on the other hand, scrambles your files to render them unusable until you pay a ransom fee to its creator.
How do you become infected by Ransomware?
Every organisation that uses the internet is vulnerable to ransomware. The majority of ransomware spread when users click on a malicious link in a spam e-mail, visiting a malicious or compromised websites and ads, or unsafe Wi‑Fi networks. Here’s how it infects your computer:
Social engineering – is tricking people into downloading malware from a fake attachment or link. Malicious files are often disguised as ordinary documents (order confirmations, receipts, bills, notices) and appear to have been sent by a reputable company or institution. Social engineering attacks are difficult for IT departments to prevent. Not because they haven’t the skills to stop an attack, but because the attacks are counting on human error.
Malvertising – is an attack in which perpetrators inject malware into legitimate online advertising (paid ads) networks. These ads deliver ransomware, spyware, viruses and other nasty things, at the click of a button.
Exploit kits – are designed to exploit vulnerabilities and security holes caused by out-of-date software. These kits were developed as a way to automatically and silently exploit vulnerabilities on victims’ computer while browsing the web. Once they gain access, the attackers can then execute code and install other pieces of malware such as ransomware.
Drive-by downloads – this is when simply viewing an innocent-looking website or watching a video is enough to cause the infection, which happens in the background and without the user’s knowledge or consent.
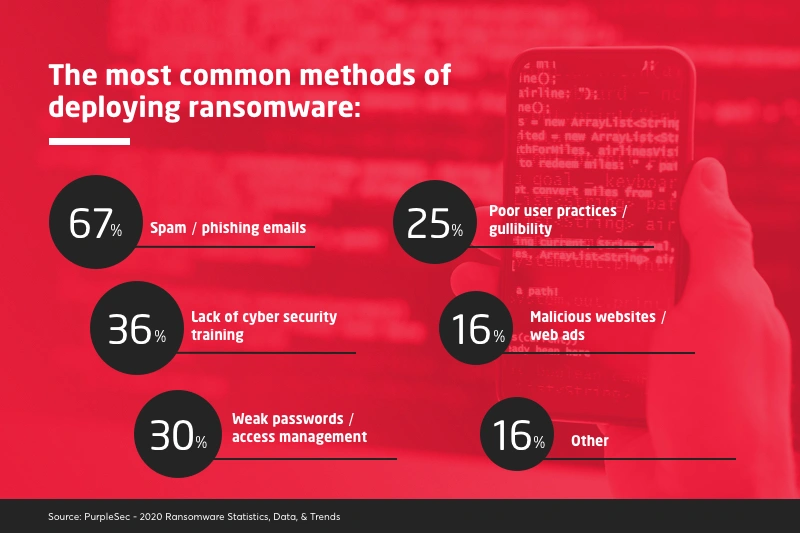
The most common methods of deploying ransomware include:
Here’s how a ransomware attack works to infect a network within an organization:
- A threat actor sends an email with an attachment to a malicious link.
- The email bypasses the spam filter hitting the users inbox.
- A user receives the malicious email and clicks a link, or downloads an attachment.
- The antivirus fails to block the threat.
- Malware XYZ.exe is delivered and the payload is executed on to the user’s machine.
- The victim’s files are encrypted by the malware.
- A ransom note is sent typically asking for payment in untraceable bitcoin.
- Attackers move laterally across an organization to spread the virus and maximize the effectiveness of the attack.
Common error messages you get are “Oops yours files have been encrypted”, “Unknown file type” or “Windows can’t open this file” (“There is no application set to open the document” for Mac).
However, by the time the ransom message pops up on a machine, it is too late to save the system. Once in place, the ransomware then locks all files it can access using strong encryption. Finally, it will demand a ransom (typically payable in Bitcoins) to decrypt the files and restore full access to the affected IT systems.
Did you know?
- 20% of ransomware victims are small to mid-sized businesses.
- The average cost per ransomware incident in 2020 is $10,400.
- 85% of MSPs report ransomware as a common threat to small to mid-sized businesses.
- 1.5 million new phishing sites are created every month.
- Ransomware made history in 2020 contributing to the first reported death related to a cyber attack.
Steps on how to mitigate the risk of ransomware attacks:
Caution is the first step to avoiding an attack
Lack of cybersecurity training and awareness contributes to 36% of the successful ransomware deployment. That is why detecting and eliminating the threat before it enters your server is a must. Exercise cyber hygiene, such as using caution when opening email attachments and links. Your best defence is following a simple rule: when in doubt, don’t visit, and don’t click.
Perhaps our article Malicious Emails: How to Recognise Them and Stay Protected can give you more understanding of how cybercriminals design malicious emails to steal your money and personal information.
Backup of your data – it’s critical
Regularly backup your servers and computers, not only with physical backups but also by using cloud servers. Using cloud services for back-up and recovery can dramatically reduce the impact of data loss.
Use a backup system that allows multiple iterations of the backups to be saved, in case a copy of the backups includes encrypted or infected files. Routinely test backups for data integrity and to ensure it is operational as well. Up-to-date back-ups make it possible to restore files without paying a ransom.
Patching
A computer software patch can be applied to a program or operating system to repair an exposed flaw. It is critical that organizations ensure that all systems have the latest patches applied to them, as this reduces the number of potential vulnerabilities within the business for an attacker to exploit. Cyber-criminals usually look for the latest uncovered exploits in the patches made available and then target systems that are not yet patched.
Here’s what patches can do:
- Address a specific bug or flaw
- Improve an OS or application’s general stability
- Fix a security vulnerability
Never use unfamiliar media
Never insert USBs or other removal storage devices into your computer if you do not know where they came from. Any malware on the USB can spread to other devices to which it is connected. Cybercriminals may have infected the device with ransomware and left it in a public space to lure you into using it.
For more tips on safe business file sharing, read this article.
We keep you protected
Computers being locked up with user files held for ransom could paralyse your business. Avoid becoming a victim of the next widespread ransomware attack by having a solid backup plan in place. Insight’s team of IT experts can help you identify cybersecurity threats and establish a consistent security posture across all parts of your IT infrastructure. We employ the latest security protocols to guarantee the best cybersecurity for your business.
If you aren’t sure whether you have enough protection in place to prevent a ransomware infection, consult one of our IT professionals today.




